Contact us. We are happy to talk about your needs and prepare an offer.
Information technology audit
ImpiCode provides IT audit services of systems and source code. We assess the quality and completeness of the code as well as the performance of IT systems and suggest changes to increase the efficiency of the analyzed solutions.
IT audit benefits

Minimizing problems
Potential threats analysis helps estimate the risk of IT system failure, as well as find solutions to prevent such difficulties.

Lower IT systems costs
Preventing problems and detecting irregularities at an early stage is cheaper than dealing with the consequences of a serious malfunction of the IT system.

Increased efficiency
Modifications made to the software may improve some processes, and thus contribute to an increase in the efficiency of employees.
Higher safety
Safety checkups enable the assessment of data safety and minimize the risk of successful cybercriminal attacks.
The IT audit includes
- checking the quality and completeness of the code,
- verification of the technical documentation and instructions,
- detection of errors in the software,
- IT systems safety analysis,
- inspection of user access and authorizations and the password authentication process,
- analysis of IT architecture and network configuration,
- software performance verification, identification of bottlenecks,
- analysis of CI/CD,
- a presentation of suggested changes that will automate or optimize processes.
When should an audit be conducted?
It’s wise to carry out an IT audit to
- confirm the quality of the delivered technological solution built by an external IT service provider,
- change the IT system,
- check the safety of stored data,
- implement a new solution that will be integrated with the current system,
- optimize the costs of maintaining IT infrastructure,
- increase the efficiency of IT systems,
- change the IT service provider.

Our clients
What is an IT audit?
An IT audit involves carrying out an analysis and assessing the functioning of IT systems. The goal of an IT audit is to determine a solution’s efficiency. Auditors also check whether the system sufficiently protects data and whether it operates in line with the adopted operational and control objectives. Conducting an audit will not only detect irregularities in safety but also improve the operation of IT systems.
Once the audit is done, the company receives a detailed report about its IT infrastructure with the weak and ineffective areas highlighted and elements that may cause problems in the future. The report also includes recommendations on increasing safety and using the current IT system more efficiently.
What is a source code audit?
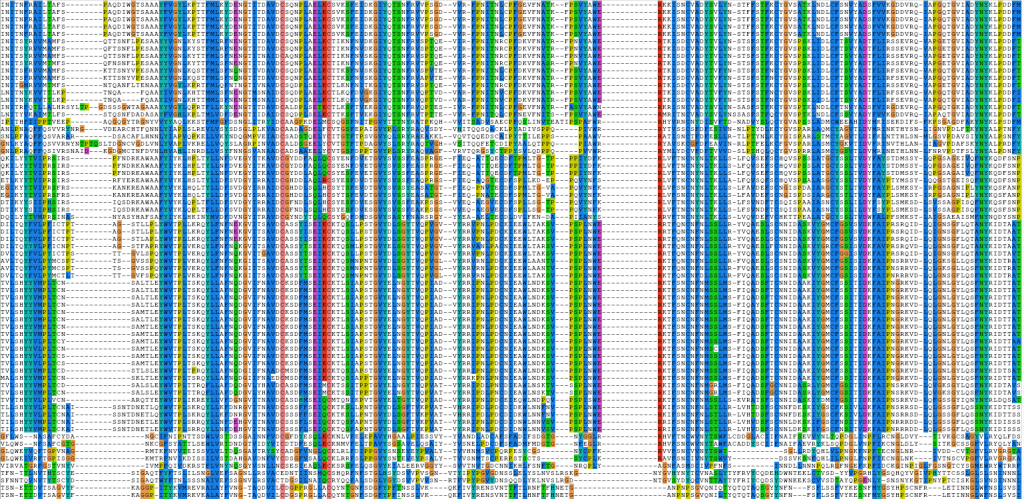
A source code audit involves examining the quality of the analyzed code, its scalability, completeness, correctness, maintainability, and stability of operation. The quality of the code is assessed by checking whether the tested code is readable and whether it was written following good coding practices. The source code audit enables to determine whether the company is struggling with so-called technological debt. This is when a company is using solutions which may cause problems in the future because the technology used is no longer supported or may not be supported soon. Code analysis also helps to check if the company is using unsupported libraries or struggling with safety errors. The auditors also determine the degree of software resistance to changes and refactoring.
The source code audit process includes various research methods and techniques, including static and dynamic code analysis and code review. First, auditors always carefully read the technical documentation of the software and its instructions. By analyzing the code, the auditors not only detect errors but also mistakes and gaps in the documentation which may increase some development and modification costs in the future.

Static code analysis involves analyzing the structure of the program without turning it on. As a result, auditors can find safety gaps. Besides this, auditors pay attention to the structures used and the coding style. Writing code in line with good practices not only helps to avoid many programming errors but also enforces certain rules of code creation and thus increases its quality, efficiency, and stability. Currently, there are many statical code analysis tools. One example is Code Climate detecting repetitions and complex constructions. The tool supports languages such as CSS, Go, JavaScript, PHP, Python, and Ruby. Another frequently used solution for debugging a Python script is Pylint.
Dynamic code analysis involves performing various tests on the turned program. Such processes not only detect errors but also test the resilience of interfaces and APIs. To perform the analysis, the program must have input data.
Types of IT audits
IT audits may be conducted on whole IT systems or focus only on selected issues. According to the purpose, there are several types of IT audits.
Software legality audit
Software legality audits detect illegal software and thus avoid high financial penalties. During the inspection, it is checked whether the way of using the software is consistent with what is included in the license. A software legality audit reduces the risk of being fined in the event of finding an illegal solution during an inspection.
Hardware audit
This type of audit provides information about equipment and how it is distributed. It checks whether all owned devices are working and need to be repaired or disposed of. A hardware audit also involves running a program on each computer that describes the hardware configuration of the computer.
Safety audit
A safety audit is used to control and monitor safety mechanisms. It checks the safety of information flow and stored data. Bear in mind, that with the technology development, new methods of cybercriminals are emerging and thus new safety measures are constantly being created. Regular safety audits minimize the risk of data leaks.
Applications and information systems audit
An applications and IT systems audit analyze and evaluate their performance, usability, scalability, and safety. Also, it helps to decide whether to maintain a given software or abandon it. Moreover, it indicates areas that require improvement.
Business processes audit
A business processes audit is performed to optimize the costs of IT systems. The main goal is to suggest solutions increasing the efficiency of the company's operations and reduce costs.
Information technology audit benefits
Each type of audit provides multiple benefits. First of all, the company receives valuable information about currently used IT systems and advice on how to increase efficiency. Below are the most important benefits of IT audit.
Increased safety
The improved safety of stored data and information is the main advantage. Audit implementation will not only reveal the least secured elements of the system that may become an easy target for cybercriminals but will also propose solutions to minimize this risk. It is easier and cheaper to prevent hacker attacks than to deal with the legal and financial consequences of a data leak. To assess the level of safety, auditors conduct penetration tests based on attempts to break into the company's system. In such a situation, the auditor is a hacker and tries to extract data. If the attempt is successful, it means the system has safety gaps which need to be fixed.
Lower costs
Auditors evaluate the IT system’s efficiency, verify the condition of all devices and software used by the company, and report any irregularities or errors. They can also advise whether the technological product is unnecessary and should be replaced with another one that generates lower costs. The audit also prevents system failures, which can be costly to repair.
Compliance with legal standards
Companies must comply with formal requirements and legal regulations, for example, related to personal data protection. Otherwise, the company will not only receive a high financial penalty but will also lose its credibility and reputation, which will probably lead to losses in customers. Conducting an audit with legal standards reassures the owners that they are adhering to all laws and regulations.
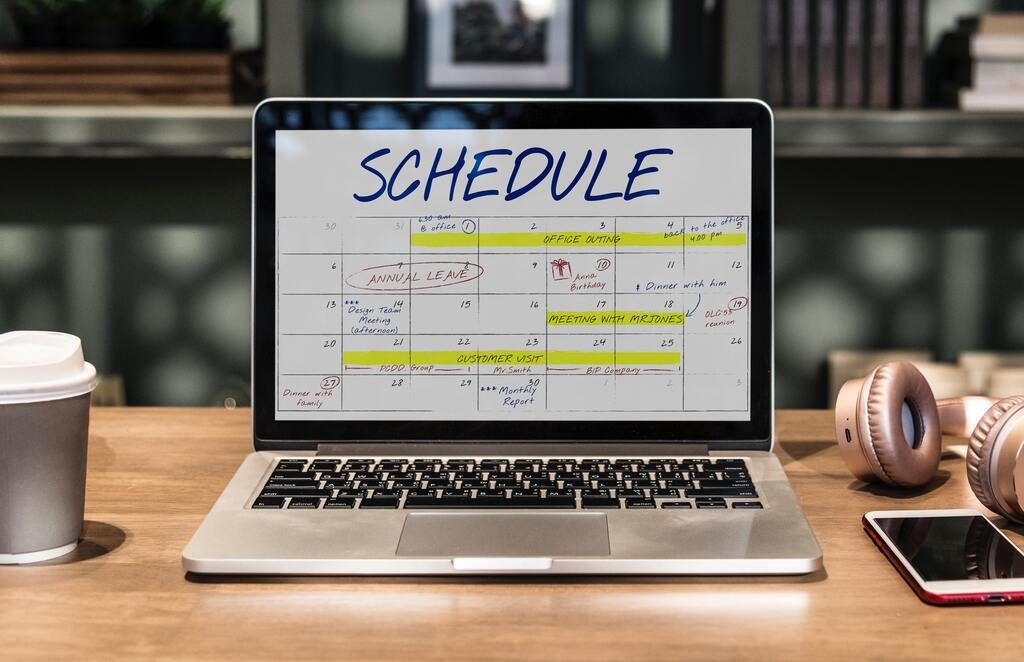
The stages of an IT audit process
The audit process is strictly defined and has several stages guaranteeing appropriate control. Below are the most significant steps needed to be accurately and reliably performed by auditors to provide the company with reliable information.
Defining the objectives and scope of the audit
After the initial introduction into the company and understanding its main needs, defining goals and the scope of the audit largely depends on the type of company. The most significant step is safety level check-ups. Additionally, auditors estimate the risk of breaking into an IT system and suggest solutions to minimize this risk. A software legality audit checks whether the company is using only legal solutions. An IT system performance audit assesses the effectiveness and suggests changes which may increase it.
Once the goals are established, the audit scope, which includes aspects such as the substantive assessment of specific system elements, the number of tests performed, and the duration of individual works, is determined.
Planning
Planning is a crucial part of the audit. It consists of proper preparations and determining the next stages. Bear in mind that planning is an ongoing process and some original plans may, and in some cases must change as new information appears. Planning also involves an initial evaluation of the IT systems operation. Additionally, auditors try to understand the functioning of the organization and learn about its needs and goals. This way, they find out which system functions are essential to the company's operations and which solutions are unnecessary.
Collection and evaluation of evidence
The auditor's opinion on specific IT architecture topics must be supported by reliable evidence obtained using various research methods. Auditors carefully review the system documentation and talk with employees, especially with IT system analysts, to better understand the functioning of the systems, control, and safety mechanisms. They also analyze the IT infrastructure and perform tests. As a result, they identify the weak points of the system.
Writing and submitting a report
The final stage of the auditor's work is to write a report specifying all the works performed, the results of the tests, and the evaluation of the functioning of the IT systems. The auditor highlights the IT infrastructure’s weaknesses, estimates the risk of specific threats, and offers solutions to improve the operation of the systems and increase their safety.
If you require an IT audit or you would just like to find out more about this topic, write to us via the contact form.